What are the 10 most dangerous Windows file types?
If you own a computer and surf the web you are a target of malicious software, or malware. These programs are designed to cause damage and/or steal your personal information. Common examples of malware include viruses that can delete files or directory information, spyware that can gather data from a computer system without your knowledge, and worms that can replicate and tunnel through your computer's memory and hard drive.
Malware can infect your computer in several different ways, but one of the most common is through an email attachment. For example, you might receive an email from an unknown user that prompts you to open an unknown file.
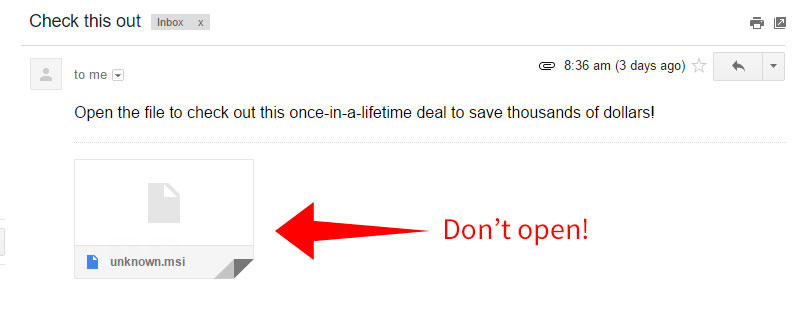
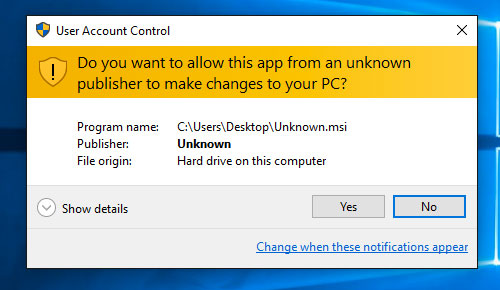
If you open the file, it can run malicious code that may install malware or run destructive scripts on your computer. Therefore, it is wise to heed the warning that Windows displays when opening unknown files or running unverified applications.
The best way to protect yourself from an email-based malware attack is to not open unknown email attachments. If you get an email from an unrecognized sender and it has an attachment, there is no reason to open it.
Of course, people may also send you legitimate email attachments that are safe to open. Therefore, it is helpful to be aware of file types (and file extensions) that are potentially dangerous.
Below is a list of 10 common Windows file types that may pose a threat to you.
1. .EXE
EXE files are one of the most popular file types in Windows. It contains an executable program, which you can easily run by double-clicking the file.
The danger: EXE files' popularity among users, importance to the Windows file system, and ease-of-use makes them the best choice for a malware attack. A common method of delivery is through an email attachment that executes a virus when you open the file.
2. .COM
A COM file is an executable program that was the original program type run by MS-DOS. It can also be run on Windows. It is saved in a binary format and is similar to an EXE file.
The danger: The COM file is commonly used for executing a set of instructions. If it contains malware and is opened, the instructions will be executed causing harm to your computer.
3. .BAT
A BAT file is a DOS batch file used to execute commands with the Windows Command Prompt (cmd.exe). It contains a series (or "batch") of commands that are executed in order. BAT files are most commonly used to start programs and run maintenance utilities within Windows.
The danger: A BAT file contains a series of line commands that will run if it is opened, which makes it a good option for malicious programmers.
4. .CMD
A CMD file is another type of batch file used by Windows. The format was introduced with Windows NT, but it can also be run by DOS. It is similar to the BAT file, but is run by CMD.EXE instead of COMMAND.COM.
The danger: The CMD file is a popular file type for writing malware. It may be used to delete data in a directory or replicate itself and open a program repeatedly to deplete a computer's resources, which slows down and crashes the system (fork bomb).
5. .MSI
An MSI file is a Windows installer package that contains installation information for a particular installer. It is often used for Windows updates and third-party software installers.
The danger: Since MSI files are usually trustworthy and commonly used for software installations, it can be difficult to spot malicious files. This provides an optimal doorway for viruses to be delivered and installed on your computer.
6. .VB / .VBS
VB and VBS files are Virtual Basic scripts written in the VBScript scripting language. They contain code that can be executed within Windows or Internet Explorer via the Windows-based script host (Wscript.exe).
The danger: These scripts are an ideal format for hiding viruses or other malware. They are often delivered as an unknown e-mail attachment that will run when opened.
7. .WS / .WSF
WS and WSF files are Window Script files, which is another scripting format supported by Windows. They contain executable scripts for Windows that use JScript or VBScript code. They run when opened if Windows Scripting Host (WSH) 2.0 or later is installed.
The danger: WS and WSF files are commonly delivered as email attachments, so do not open a WS or WSF file unless you can verify its integrity.
8. .SCF
An SCF file is a Windows Explorer command used to perform an action such as moving up or down a directory or showing the Desktop. It can be run via Internet Explorer.
The danger: Since the file is a Windows Explorer command file it can be used to tell Windows Explorer to execute commands that are dangerous to your computer.
9. .SCR
An SCR file is a screensaver file for Windows used to display vector graphic or text animations, play slide shows, animation, or videos, and may include sound effects when a computer is inactive for a customized period of time.
The danger: Screensaver files contain executable code, which makes it possible for programmers to hide malicious code inside them. Since SCR files are commonly used for screensavers, it can be difficult to recognize a malicious one.
10. .PIF
Normally, a PIF file contains information that defines how an MS-DOS-based program should run. It can also be used as a shortcut to an executable file, much like an .LNK file.
The danger: Windows analyzes PIF files with the ShellExecute function and may run them as executable programs. Therefore, a PIF file can be used to transmit viruses or other harmful scripts.
So how do I avoid malware?
In this digital age, malware is always a threat. You may be a target, whether you know it or not. Therefore, it is vital to be aware of potentially harmful file formats. And remember — don't open email attachments from unknown users! It is also a good idea to use antivirus software that can detect and remove malware before it has a chance to run.