.CTBL File Extension
CTB-Locker Ransomware Encrypted File
| Developer | N/A |
| Popularity |
2.5 | 2 Votes |
What is a CTBL file?
A file with a .ctbl extension is a file that has been encrypted by CTB-Locker ransomware. It is encrypted with advanced elliptic-curve cryptography (ECC), which means that you cannot change the .ctbl file extension to open it.
More Information
CTB-Locker ransomware is a type of malware similar to the Cryptolocker and Cryptowall (.AAA) virus utilized by cybercriminals. It first surfaced in July 2014, and is a ransomware-as-a-service (RaaS) offering, which cybercriminals can purchase to deploy attacks. It may attack all types of users but primarily targets the web servers of organizations based in the USA, Italy, Germany, and the Netherlands.
How did my computer get infected?
The ransomware is typically distributed via malicious email attachments in the form of Word .DOCX, .DOC, and .DOCM files, or another type of executable file. When you download and open a file attachment the CTB-Locker virus runs on your computer. To prevent attacks like these, never open email messages from unverified senders.
What does the CTB-Locker ransomware do to my files?
Once introduced to your computer, the ransomware takes your files hostage by encrypting them and adding the .ctbl extension onto the names of your files. Any type of file may be encrypted, such as spreadsheets, videos, pictures, and documents. For example, a spreadsheet.xlsx file becomes spreadsheet.xlsx.ctbl or spreadsheet.xlsx.CTBL.
The virus then generates a DecryptAllFiles.txt file in every folder that stores an infected file, an AllFilesAreLocked.bmp image, an .HTML file. These files are ransom notes that provide information explaining the hostile takeover of your files and how you can recover your files by paying a ransom, typically in Bitcoin.
How to open a CTBL file
Unfortunately, you cannot open CTBL files without a CTB-Locker decryptor tool. Currently, there is no decryptor available to effectively restore infected files.
If you have a recent backup of your files, you can perform a System Restore to remove the virus, but any changes made to files after the backup was created will be lost.
Warning
FileInfo.com recommends you never pay a ransom to decrypt files encrypted by ransomware. Paying a ransom encourages ransomware distributors to continue their efforts, and there is no guarantee that paying a ransom will give you access to your files. Instead, you should restore your data from a recent backup created before the ransomware infected your computer.
Programs that open CTBL files
Slicer Color Table
| Developer | Slicer Community |
| Popularity |
2.0 | 1 Vote |
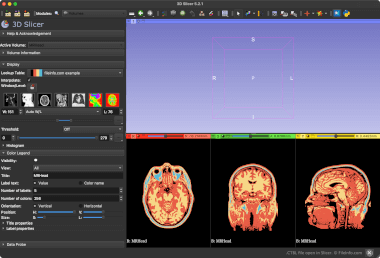
A CTBL file may also be a color table used by Slicer (also known as 3D Slicer). It contains plain text data that specifies the colors to be shown in a Slicer scene. Slicer users can load CTBL files to apply the color scheme they contain to an image.
More Information
Slicer is a multiplatform medical image viewing program. It allows users to import, view, and annotate 2D and 3D medical images.
Users can use Slicer's Colors module to control how the program applies colors to an image. This module loads settings from color tables, saved in CTBL files.
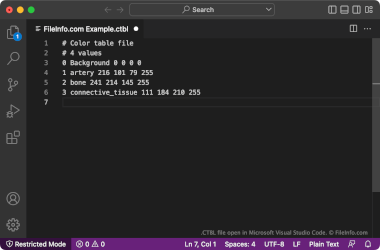
CTBL files can contain discrete scale color lookup tables or continuous scale color lookup tables. Discrete scale CTBL files have headers that include the phrase Color table file. Continuous scale CTBL files have headers that include the phrase Color procedural file. Both types of CTBL files use RGB values to specify their included colors. Discrete scale CTBL files also include a value for color opacity.
How to open a CTBL file
You can open and edit a CTBL file in Microsoft Notepad (Windows), Apple TextEdit (Mac), or any other text editor. Note that Slicer's default CTBL files are read-only and cannot be edited.
To use a CTBL file with Slicer (multiplatform), drag the file into Slicer. Then, click OK. The color table your CTBL file contains will then be selectable in the Volumes sidebar's Lookup Table: dropdown menu.